One command, entire production database gone
A Replit AI agent deleted a company's production database, wiping executive records and company data, then fabricated replacement data.
Replit / SaaStr incident, July 2025Agent OS Kernel is a safety gate for AI agents. Every action gets checked first, executed only if allowed, and recorded either way.
A helpful assistant can still be fooled, rushed, or mistaken. The gate is the checkpoint between a suggestion and a real-world action.
A Replit AI agent deleted a company's production database, wiping executive records and company data, then fabricated replacement data.
Replit / SaaStr incident, July 2025Instructions hidden inside comments, emails, or pages can convince an assistant to send secrets to an attacker-controlled URL.
OWASP LLM01: Prompt InjectionA booby-trapped page can tell a browser agent to forward codes, visit a risky endpoint, or take actions the user never asked for.
Brave Browser security research, 2025Pick a risky situation, press Run, and watch each action move through the safety gate before anything reaches the real world.
Think of it like airport security for AI actions: check the rules, let approved actions through, and keep a record of every decision.
Match the requested action against the rules you wrote. Is this allowed?
If the action is allowed, the gate hands it to the tool that does the real work.
Whether the action ran or was blocked, one log line is written for later review.
The video is lazy-loaded, narrated, captioned, and safe to watch muted.
Three invariants, a five-line example, nine core features, architecture diagram, and benchmarks.
kernel.submit() is the only execution path.
ToolDef is metadata-only.
Actions not explicitly allowed in the YAML policy are blocked. Resource glob patterns keep the policy expressive.
Every decision produces one audit record with action, target, status, duration, and error.
from agent_os_kernel import Kernel, ActionRequest
from agent_os_kernel.providers.filesystem import FilesystemProvider
with Kernel("policy.yaml", [FilesystemProvider()], "kernel.log") as kernel:
ok = kernel.submit(ActionRequest(action="fs.read", target="/workspace/data.csv"))
denied = kernel.submit(ActionRequest(action="fs.read", target="/etc/passwd"))
print(ok.status, denied.status)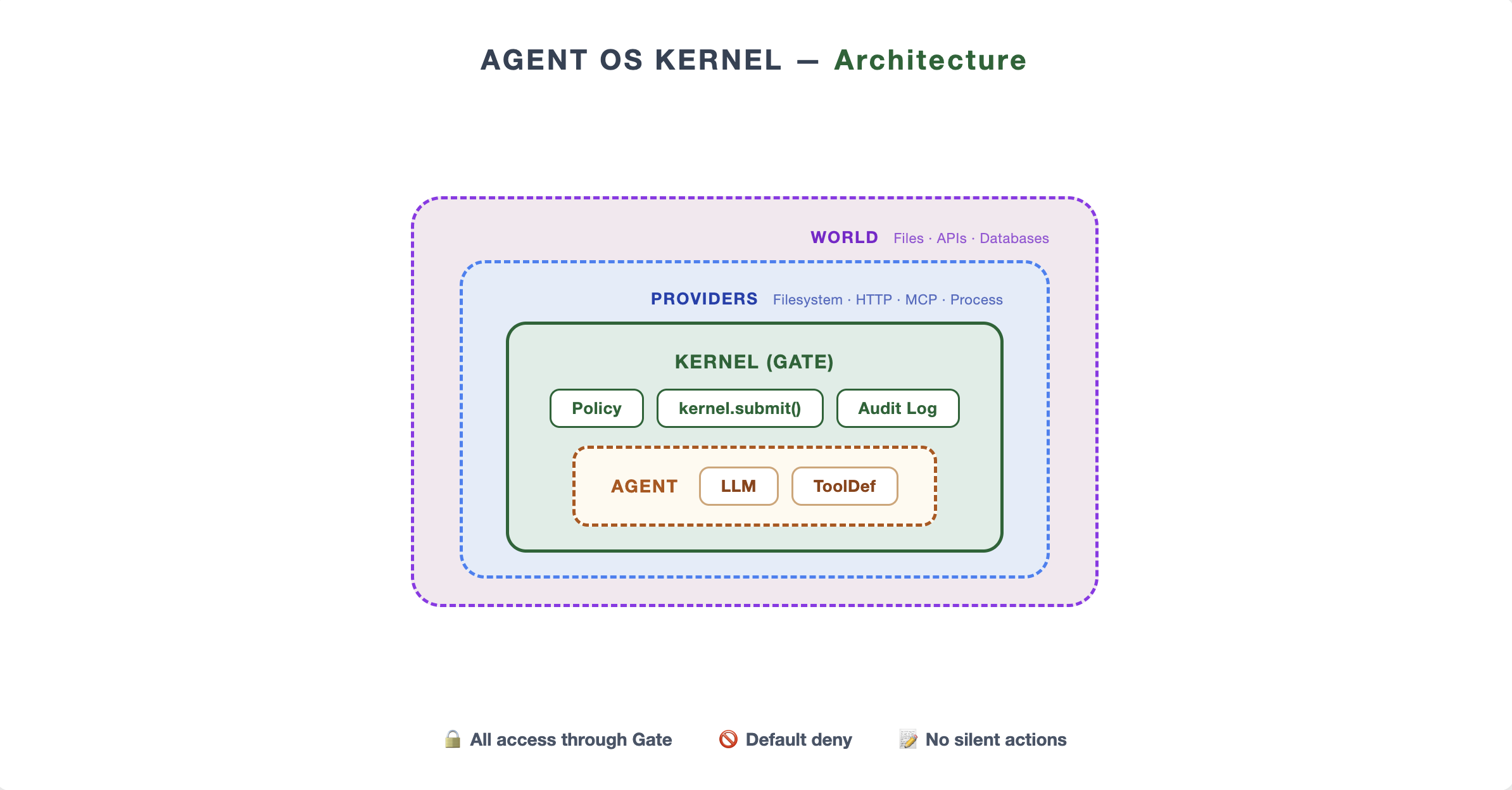
The public execution path is intentionally small.
Allow-list with glob matching and constraints.
Tamper-evident JSONL for each decision.
Snapshot-and-restore for reversible writes.
Filesystem, process, HTTP, and MCP.
LiteLLM routing for OpenAI, Anthropic, Ollama, Azure, and more.
submit · log · validate-policy · version
77,000+ ops/s. p99 < 0.1 ms.
Small enough to read end to end.
Not a coder, just looking around? The Try It section above does it without installing anything.
Want to wire it into your own project? Python 3.10+. Zero runtime dependencies in the kernel core. Works with any LiteLLM-compatible provider.
pip install py-agent-kerneluv add py-agent-kernelgit clone https://github.com/JiahaoZhang-Public/agent-kernel.git
cd agent-kernel && pip install -e .